Cosmic Node Start 317-794-0655 Unlocking Caller Data Research
The discussion centers on analyzing caller data with a focus on privacy and governance. It examines metadata, timing, routing traces, and destination patterns to surface risk signals without exposing personal details. Ethical safeguards and consent-bound practices anchor the approach, with governance and transparency guiding each step. The aim is practical, policy-ready insights grounded in data minimization. Key questions remain about implementation, accountability, and how stakeholders should proceed as complexities emerge.
What Is “Unlocking Caller Data” and Why It Matters
Unlocking caller data refers to the process of accessing and interpreting information associated with telephone calls, such as caller identity, call timing, duration, and related metadata. It enables organizations to derive unlocking data without overreach, yielding caller insights while respecting privacy. Attention to metadata patterns and risk signals guides responsible use, balancing transparency with safeguards for freedom and security.
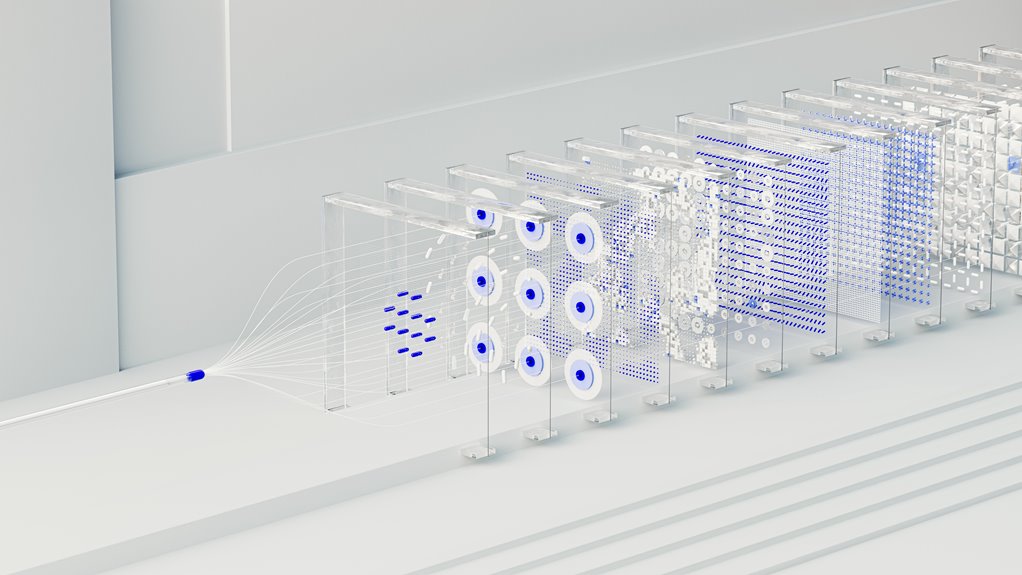
How Metadata and Call Routing Reveal Patterns and Risk Signals
Metadata and call routing are instrumental in identifying patterns and risk signals within caller data. The discussion emphasizes how metadata layers—timing, sequence, and destination—facilitate pattern analysis and anomaly detection. Call routing traces illuminate pathways, revealing consistency or deviation in behavior. Careful interpretation avoids overreach, focusing on signal quality, context, and stability to discern actionable risk indicators without speculative conclusions.
Ethical Safeguards, Privacy Controls, and Responsible Use
Ethical safeguards, privacy controls, and responsible use are essential anchors in the analysis of caller data. The study emphasizes unlocking data within consented boundaries, applying privacy safeguards, and maintaining transparency. It advocates responsible analytics, minimal data retention, and auditability. Policy implications guide governance, ensuring rights are protected while enabling insight, accountability, and freedom to innovate without compromising trust.
Practical Steps to Study Caller Data Responsibly and Craft Policy-Ready Insights
How can researchers proceed to study caller data in a disciplined, policy-aligned manner while preserving trust? They should implement rigorous governance, transparent provenance, and ongoing stakeholder engagement, emphasizing caller data ethics and accountability.
Employ data minimization, purpose limitation, and robust de-identification.
Document methods clearly to enable policy-ready insights, while preserving freedom of inquiry and ensuring auditable, risk-aware practices across the data lifecycle.
Conclusion
Conclusion:
In examining caller data, the study tracks timing, sequence, destination, and routing with disciplined restraint; in tracing patterns, it seeks anomalies, signals, and risk indicators with measured care. In applying safeguards, it preserves privacy, enforces consent, and upholds governance; in delivering insights, it ensures transparency, accountability, and policy relevance. In balancing stewardship, it minimizes exposure, limits purpose, and documents methods; in shaping practice, it informs responsible policy and prudent, enduring operations.