Face Check ID – Ensure Security and Legitimacy in the Cybernetic Geography
Scams involving document fraud and illicit money transactions are becoming more common, profoundly affecting sectors. The businesses notify their research about effective preventive methods. There are now several alternatives available for biometric authentication. Nonetheless, using neural networks and artificial intelligence in sophisticated check procedures has increased their precision.
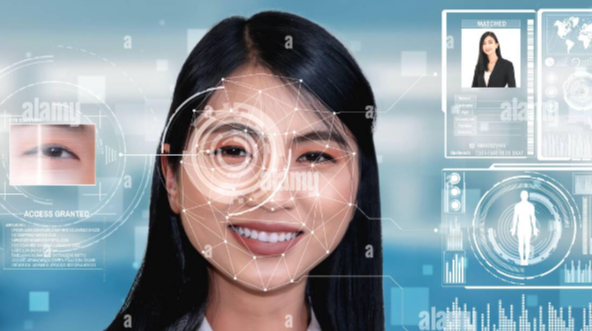
Adopting recent AI advancements is crucial to preventing real-time fraud and lowering risk factors to safeguard enterprises. The face check ID is a trustworthy and effective identity verification tool that thwarts fraud and conforms to legal specifications.
Real-Time Crimes and Digital Market
According to the survey, the electronics market is expected to grow by 125% by 2030. The anticipated growth rate is also included in this ten-year forecast., which is $16.74 billion, a notable increase in the automated virtual transaction system.
A thorough explanation of the photo ID validation is covered below. Read the article to learn about face ID checks and how businesses benefit from integrating innovative technology into their daily operations.
Quick Insight into Photo Identity Verification and Face Check Services
Photo ID verification stands for identification checking algorithms used to compare the observable recognition of the entity. The features of the face, including the eyes, cheekbone outlines, nose, lips, and forehead, can be extracted by face-checking systems. Once completed, the photo ID verification recognizes the countenance and compares it to the facial features in the data warehouses.
See Also “Unlocking Digital Excellence: Kpn, Simyo, Digital Heroes, First Class Internet, Snelpakkers
Gains of Face Check Solutions
The main advantages of photo verification services are listed below.
- Integrating the check methods is straightforward.
- They work with even the most energy-efficient cameras.
- With the best accuracy rate and security measures, it moves forward with the details.
- It improves customer experience and functions best when combined with user onboarding tactics.
How Face ID Verification Works?
Face detection functions by recognizing the features on the face in both the picture and the video. It also delivers quick, accurate results and functions well with silicon mask detection. Facial recognition is a quick, adaptable method with facilities that are tailored for it. With its smooth integration capabilities, the cutting-edge facial recognition technology works well with the current infrastructures. The technique is accessible globally and offers fully automated solutions.
Face Check ID Strengthening the Digital Validation Systems
Calculating Inaccuracies in Results
When face checks are integrated into manufacturing and retailing businesses, their effectiveness may be evaluated. These companies now employ the most effective detection technique against sophisticated criminal operations: powerful visual inspection software driven by NN and AI. Modern technologies can detect even the most negligible product flaws with the integration of facial verification. It is determined by looking at the deep learning models that the verification approach performs best when errors are identified.
Confirming Voice with Face Check ID
The businesses can get help from the deep learning algorithms in differentiating between unique individual tones by using matrix training approaches. An individual’s voiceprints are kept for future reference in data warehouses. On the other hand, it functions by confirming the individual’s identification while comparing the voice to the recorded information. It is frequently applied as an additional layer of protection against fraud and impersonation.
Utilize Pre-trained Models
Since the pre-trained patterns of identity verification use fewer resources and are therefore more economical, they are more efficient. These models already include a variety of techniques for improving online face recognition. On the other hand, there is a greater possibility of adjusting the face-check approaches when using specified algorithms. But it also makes the system more accurate, which lowers the chance of mistakes.
Built Neural Networks
In essence, neural networks (NNs) allow a system to comprehend artificial intelligence (AI) algorithms and adjust its operation accordingly. The automated system’s smooth integration of neural networks has made online check services possible. In contrast to pre-defined procedures, deep learning systems only require a limited number of photos, and efficient solutions require image processing in the training sample.
Identifying Entities and Their Activities
These days, sophisticated NN and ML programs enable the analysis of activity detection and separating items that differ from people. Face recognition deep learning detection systems are effective enough to quickly identify user emotions using human intelligence recorded by the cameras. They can also recognize neutral expressions on the face.
Final Words
Artificial intelligence and deep learning algorithms are advancing toward natural processing languages to make them more user-friendly and power the efficient face check method. The updated techniques enable remote security monitoring and onboarding of new business entities. These days, corporations have more prominent and visible fields that allow imposters to create new ways to harm the company utilizing cutting-edge tactics.
Robust identity verification software, such as Face Check ID, helps digital firms grow and stay credible in the marketplace over time. Furthermore, using genuine face-checking techniques is essential to prevent identity theft and impersonation with unauthorized access. It functions best with law enforcement agencies and enhances the retailing experience.



